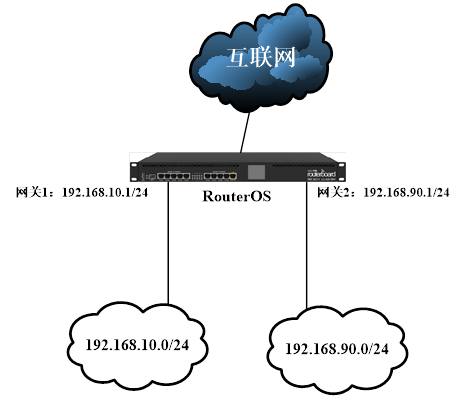
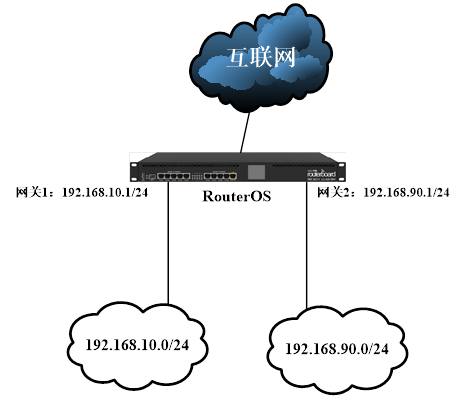
 RouterOS内网有192.168.10.0/24和192.168.90.0/24两个网段,网关都配置在RouterOS内口ether2和ether3,IP地址配置:
/ip address
add address=192.168.10.1/24 interface=ether2
add address=192.168.90.1/24 interface=ether3
由于两个网段涉及特殊业务,不能相互访问,需要通过防火墙filter控制两个段的互访问控制IP段访问,进入ip firewall filter中添加一条forward规则为:
/ip firewall filter add chain=forward src-address=192.168.10.0/24 dst-address=192.168.90.0/24 action=drop
但在网络里希望192.168.10.8/32的主机访问192.168.90.0/24的网络
/ip firewall filter add chain=forward src-address=192.168.10.8/32 dst-address=192.168.90.0/24 action=accept
查看fliter配置
[admin@MikroTik] /ip firewall filter> print
Flags: X - disabled, I - invalid, D - dynamic
0 chain=forward action=drop src-address=192.168.10.0/24 dst-address=192.168.90.0/24 log=no log-prefix=""
1 chain=forward action=accept src-address=192.168.10.8/32 dst-address=192.168.90.0/24 log=no log-prefix=""
通过move命令将允许192.168.10.8主机访问192.168.90.0/24段规则移动到序列最上,即”0”,优先执行,将1规则移动到0
[admin@MikroTik] /ip firewall filter> move 1 0
[admin@MikroTik] /ip firewall filter> print
Flags: X - disabled, I - invalid, D - dynamic
0 chain=forward action=accept src-address=192.168.10.8/32 dst-address=192.168.90.0/24 log=no log-prefix=""
1 chain=forward action=drop src-address=192.168.10.0/24 dst-address=192.168.90.0/24 log=no log-prefix=""
RouterOS内网有192.168.10.0/24和192.168.90.0/24两个网段,网关都配置在RouterOS内口ether2和ether3,IP地址配置:
/ip address
add address=192.168.10.1/24 interface=ether2
add address=192.168.90.1/24 interface=ether3
由于两个网段涉及特殊业务,不能相互访问,需要通过防火墙filter控制两个段的互访问控制IP段访问,进入ip firewall filter中添加一条forward规则为:
/ip firewall filter add chain=forward src-address=192.168.10.0/24 dst-address=192.168.90.0/24 action=drop
但在网络里希望192.168.10.8/32的主机访问192.168.90.0/24的网络
/ip firewall filter add chain=forward src-address=192.168.10.8/32 dst-address=192.168.90.0/24 action=accept
查看fliter配置
[admin@MikroTik] /ip firewall filter> print
Flags: X - disabled, I - invalid, D - dynamic
0 chain=forward action=drop src-address=192.168.10.0/24 dst-address=192.168.90.0/24 log=no log-prefix=""
1 chain=forward action=accept src-address=192.168.10.8/32 dst-address=192.168.90.0/24 log=no log-prefix=""
通过move命令将允许192.168.10.8主机访问192.168.90.0/24段规则移动到序列最上,即”0”,优先执行,将1规则移动到0
[admin@MikroTik] /ip firewall filter> move 1 0
[admin@MikroTik] /ip firewall filter> print
Flags: X - disabled, I - invalid, D - dynamic
0 chain=forward action=accept src-address=192.168.10.8/32 dst-address=192.168.90.0/24 log=no log-prefix=""
1 chain=forward action=drop src-address=192.168.10.0/24 dst-address=192.168.90.0/24 log=no log-prefix=""
分类:IP/IPv6
发布于 2019-04-20 18:27:25 +0800 CST
当RouterOS作为网关,并在RouterOS的内口配置多个IP地址段(通常用于VLAN区分不同的办公段、核心设备或区域划分)连接多个IP子网段,当我们需要控制多个IP网段之间的访问时,需通过防火墙filter来完成。通过下面一个简单实例介绍:
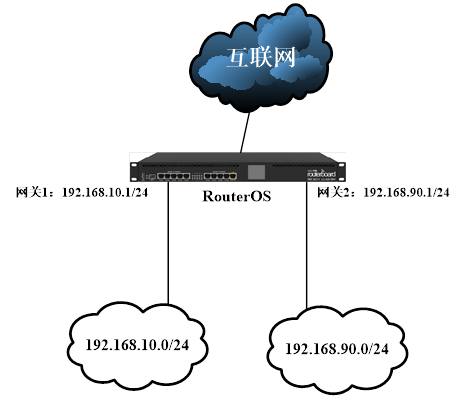 RouterOS内网有192.168.10.0/24和192.168.90.0/24两个网段,网关都配置在RouterOS内口ether2和ether3,IP地址配置:
/ip address
add address=192.168.10.1/24 interface=ether2
add address=192.168.90.1/24 interface=ether3
由于两个网段涉及特殊业务,不能相互访问,需要通过防火墙filter控制两个段的互访问控制IP段访问,进入ip firewall filter中添加一条forward规则为:
/ip firewall filter add chain=forward src-address=192.168.10.0/24 dst-address=192.168.90.0/24 action=drop
但在网络里希望192.168.10.8/32的主机访问192.168.90.0/24的网络
/ip firewall filter add chain=forward src-address=192.168.10.8/32 dst-address=192.168.90.0/24 action=accept
查看fliter配置
[admin@MikroTik] /ip firewall filter> print
Flags: X - disabled, I - invalid, D - dynamic
0 chain=forward action=drop src-address=192.168.10.0/24 dst-address=192.168.90.0/24 log=no log-prefix=""
1 chain=forward action=accept src-address=192.168.10.8/32 dst-address=192.168.90.0/24 log=no log-prefix=""
通过move命令将允许192.168.10.8主机访问192.168.90.0/24段规则移动到序列最上,即”0”,优先执行,将1规则移动到0
[admin@MikroTik] /ip firewall filter> move 1 0
[admin@MikroTik] /ip firewall filter> print
Flags: X - disabled, I - invalid, D - dynamic
0 chain=forward action=accept src-address=192.168.10.8/32 dst-address=192.168.90.0/24 log=no log-prefix=""
1 chain=forward action=drop src-address=192.168.10.0/24 dst-address=192.168.90.0/24 log=no log-prefix=""
RouterOS内网有192.168.10.0/24和192.168.90.0/24两个网段,网关都配置在RouterOS内口ether2和ether3,IP地址配置:
/ip address
add address=192.168.10.1/24 interface=ether2
add address=192.168.90.1/24 interface=ether3
由于两个网段涉及特殊业务,不能相互访问,需要通过防火墙filter控制两个段的互访问控制IP段访问,进入ip firewall filter中添加一条forward规则为:
/ip firewall filter add chain=forward src-address=192.168.10.0/24 dst-address=192.168.90.0/24 action=drop
但在网络里希望192.168.10.8/32的主机访问192.168.90.0/24的网络
/ip firewall filter add chain=forward src-address=192.168.10.8/32 dst-address=192.168.90.0/24 action=accept
查看fliter配置
[admin@MikroTik] /ip firewall filter> print
Flags: X - disabled, I - invalid, D - dynamic
0 chain=forward action=drop src-address=192.168.10.0/24 dst-address=192.168.90.0/24 log=no log-prefix=""
1 chain=forward action=accept src-address=192.168.10.8/32 dst-address=192.168.90.0/24 log=no log-prefix=""
通过move命令将允许192.168.10.8主机访问192.168.90.0/24段规则移动到序列最上,即”0”,优先执行,将1规则移动到0
[admin@MikroTik] /ip firewall filter> move 1 0
[admin@MikroTik] /ip firewall filter> print
Flags: X - disabled, I - invalid, D - dynamic
0 chain=forward action=accept src-address=192.168.10.8/32 dst-address=192.168.90.0/24 log=no log-prefix=""
1 chain=forward action=drop src-address=192.168.10.0/24 dst-address=192.168.90.0/24 log=no log-prefix=""
 RouterOS内网有192.168.10.0/24和192.168.90.0/24两个网段,网关都配置在RouterOS内口ether2和ether3,IP地址配置:
/ip address
add address=192.168.10.1/24 interface=ether2
add address=192.168.90.1/24 interface=ether3
由于两个网段涉及特殊业务,不能相互访问,需要通过防火墙filter控制两个段的互访问控制IP段访问,进入ip firewall filter中添加一条forward规则为:
/ip firewall filter add chain=forward src-address=192.168.10.0/24 dst-address=192.168.90.0/24 action=drop
但在网络里希望192.168.10.8/32的主机访问192.168.90.0/24的网络
/ip firewall filter add chain=forward src-address=192.168.10.8/32 dst-address=192.168.90.0/24 action=accept
查看fliter配置
[admin@MikroTik] /ip firewall filter> print
Flags: X - disabled, I - invalid, D - dynamic
0 chain=forward action=drop src-address=192.168.10.0/24 dst-address=192.168.90.0/24 log=no log-prefix=""
1 chain=forward action=accept src-address=192.168.10.8/32 dst-address=192.168.90.0/24 log=no log-prefix=""
通过move命令将允许192.168.10.8主机访问192.168.90.0/24段规则移动到序列最上,即”0”,优先执行,将1规则移动到0
[admin@MikroTik] /ip firewall filter> move 1 0
[admin@MikroTik] /ip firewall filter> print
Flags: X - disabled, I - invalid, D - dynamic
0 chain=forward action=accept src-address=192.168.10.8/32 dst-address=192.168.90.0/24 log=no log-prefix=""
1 chain=forward action=drop src-address=192.168.10.0/24 dst-address=192.168.90.0/24 log=no log-prefix=""
RouterOS内网有192.168.10.0/24和192.168.90.0/24两个网段,网关都配置在RouterOS内口ether2和ether3,IP地址配置:
/ip address
add address=192.168.10.1/24 interface=ether2
add address=192.168.90.1/24 interface=ether3
由于两个网段涉及特殊业务,不能相互访问,需要通过防火墙filter控制两个段的互访问控制IP段访问,进入ip firewall filter中添加一条forward规则为:
/ip firewall filter add chain=forward src-address=192.168.10.0/24 dst-address=192.168.90.0/24 action=drop
但在网络里希望192.168.10.8/32的主机访问192.168.90.0/24的网络
/ip firewall filter add chain=forward src-address=192.168.10.8/32 dst-address=192.168.90.0/24 action=accept
查看fliter配置
[admin@MikroTik] /ip firewall filter> print
Flags: X - disabled, I - invalid, D - dynamic
0 chain=forward action=drop src-address=192.168.10.0/24 dst-address=192.168.90.0/24 log=no log-prefix=""
1 chain=forward action=accept src-address=192.168.10.8/32 dst-address=192.168.90.0/24 log=no log-prefix=""
通过move命令将允许192.168.10.8主机访问192.168.90.0/24段规则移动到序列最上,即”0”,优先执行,将1规则移动到0
[admin@MikroTik] /ip firewall filter> move 1 0
[admin@MikroTik] /ip firewall filter> print
Flags: X - disabled, I - invalid, D - dynamic
0 chain=forward action=accept src-address=192.168.10.8/32 dst-address=192.168.90.0/24 log=no log-prefix=""
1 chain=forward action=drop src-address=192.168.10.0/24 dst-address=192.168.90.0/24 log=no log-prefix=""
打赏支持
微信

支付宝
